Presentation Decks
A journey from complexity to observability
AWS Community Day, Dublin, May 25th, 2023
From complexity to observability using OpenTelemetry
CloudConf, Turin, May 16th, 2023
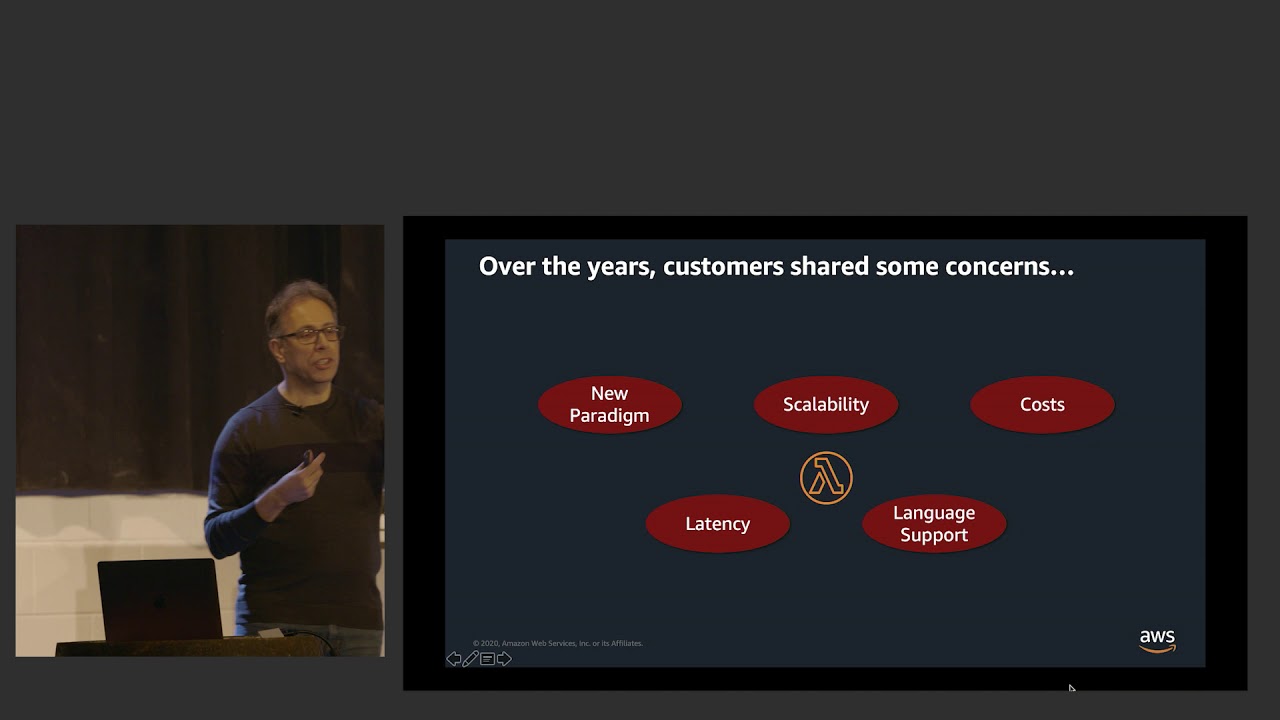
Using container images with serverless functions... and containers!
ServerlessDays Warsaw, October 20th, 2021
What Can You Do with Serverless – In 2021
NE:Tech Meetup, July 8th, 2021